The Kublr Platform automates deployment and management of secure, enterprise-grade Kubernetes clusters across multiple environments. Deploy on top of existing infrastructure or integrate with the underlying APIs to ensure consistency across all deployments, minimizing human error that may cause startup and runtime failures. Additionally, environment-specific API integration enables node autoscaling.
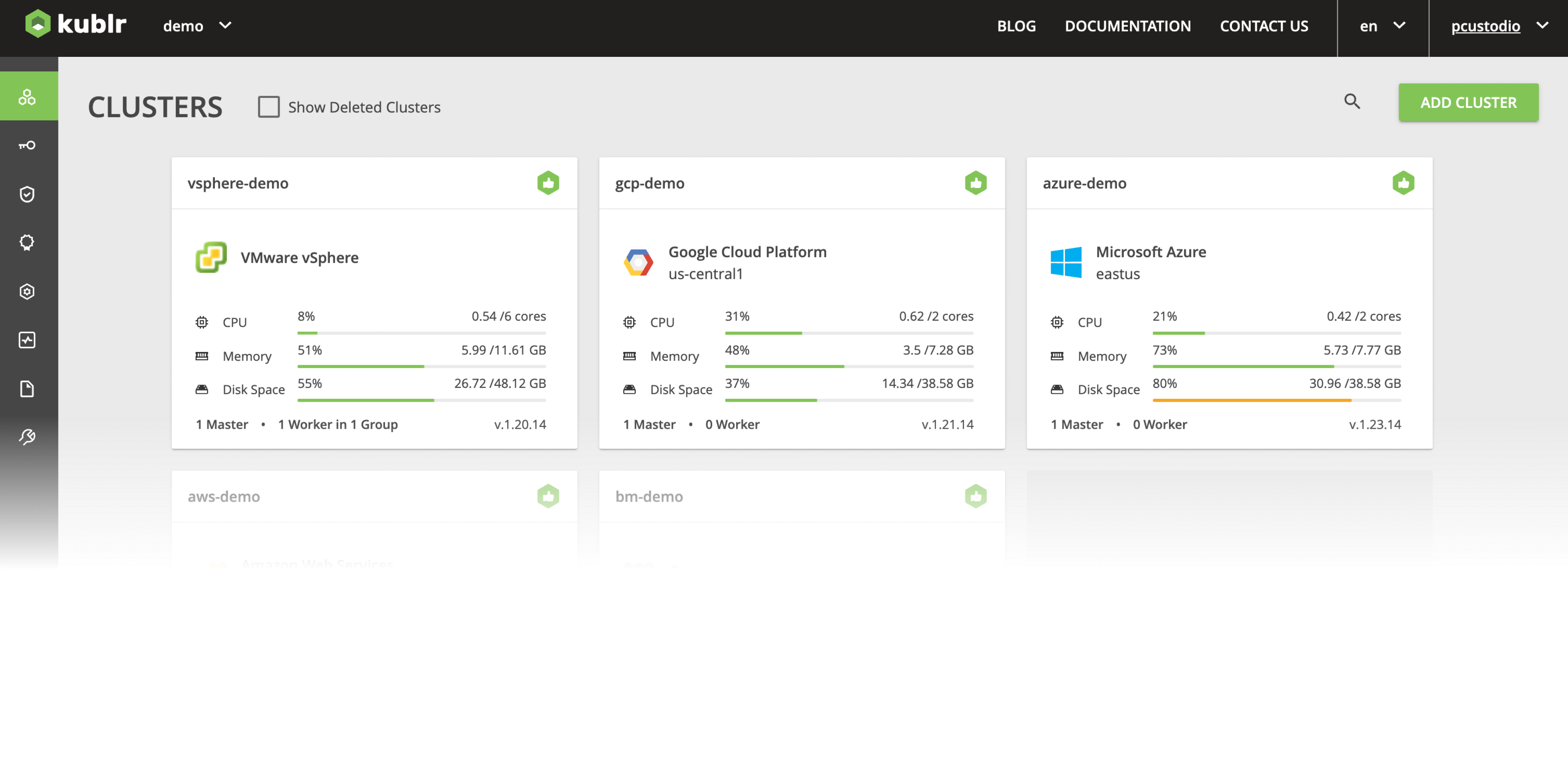
Through the Kublr UI or Custom Cluster Specification, administrators define their cluster configurations including the number of master and worker nodes, the size of these nodes, node auto-scaling where supported, ingress and other parameters. Kublr packages the configuration specification into the appropriate template for the respective cloud – Cloud Formation for AWS, Azure Resource Management (ARM) templates for Azure and templates for GCP. Kublr then lets the cloud provider provision the infrastructure and, when ready, deploys the Kubernetes cluster.
Kubernetes’ high availability and self-healing capabilities enhance integrations with the cloud provider’s infrastructure APIs. Kublr integrates cloud provider infrastructure automation tools with the Kublr Agent enabling clusters to auto-heal and self-recover in a wide range of infrastructure failure scenarios.
Cloud-hosted Kubernetes limits configuration options — there’s no control over the master nodes or visibility into master data needed to troubleshoot. Kublr clusters, on the other hand, are highly configurable. Users have complete control over cluster specification, which can be critical for a variety of use cases.
Kublr’s built-in identity broker can be integrated with enterprise identity and access management solutions like AD, via LDAP, SAML or OIDC/OAuth protocols, enabling better control of organizational resources and permissions by maintaining a single IAM repository.
To meet security requirements, users can also deploy Kubernetes into existing subnets, VPC, vnets and security groups through the UI or custom cluster specification.