Kublr also extends, without modification or forking, open-source, upstream Kubernetes capabilities, improving its resilience and security.
Kubernetes + Kublr Architecture
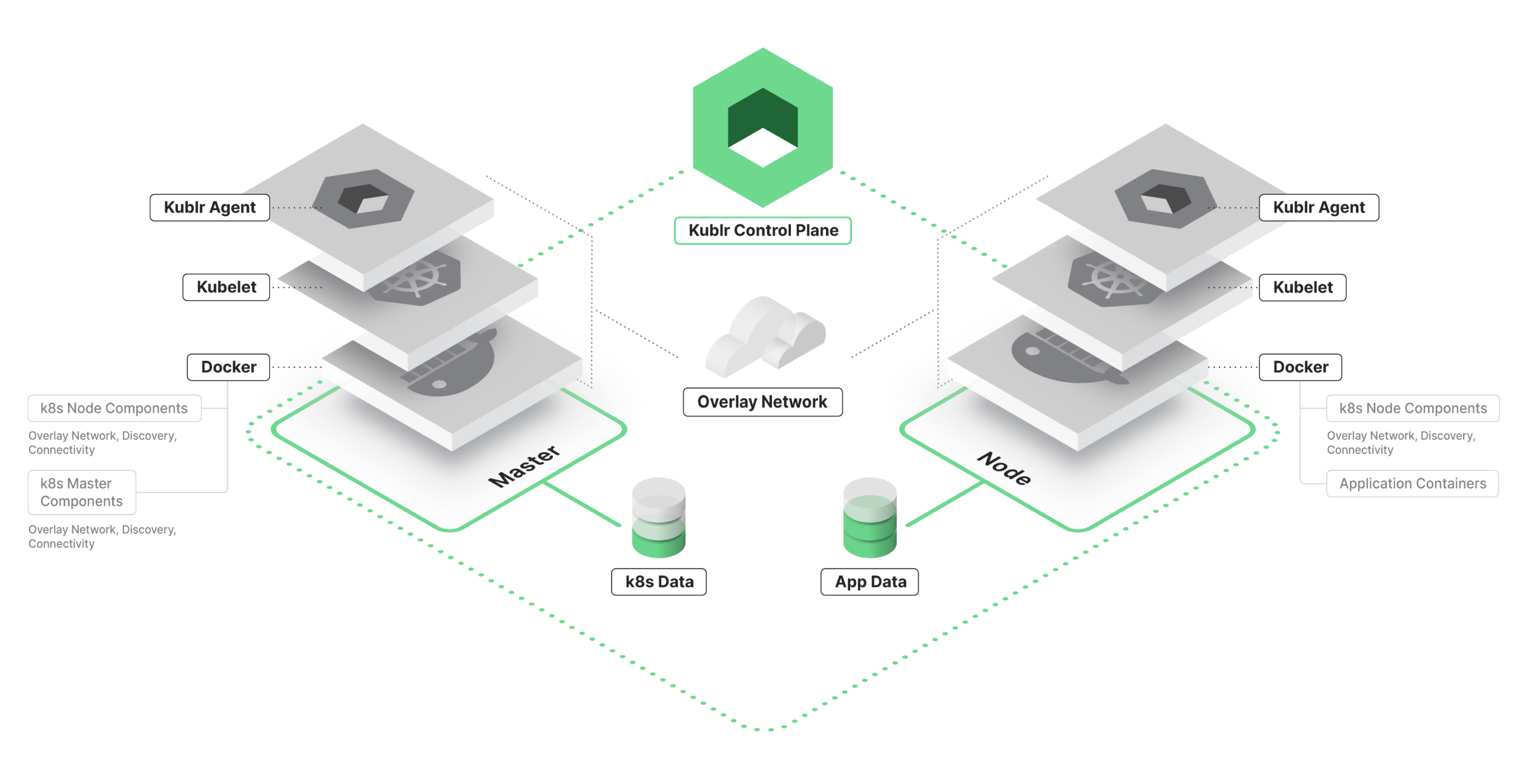
Kublr configures and manages each layer of a Kubernetes deployment, including the infrastructure, components and additional functionality on top of Kubernetes.
Kublr at the Infrastructure Layer

At the infrastructure layer, Kublr installs and configures master and worker nodes and each of the operating system, networking and Kubernetes components required for a proper Kubernetes installation.
If an infrastructure provider supports automation, Kublr provisions all the required resources and configures them in a self-healing manner.
Kublr at the Kubernetes Layer
At the Kubernetes layer, Kublr works by setting up and connecting Kubernetes components on each instance so that communication between them is secure, reliable and able to recover from failure.
Kublr uses unmodified standard Kubernetes components, direct from Google repositories and Kubernetes configuration best practices to ensure secure, reliable and standard conformant Kubernetes setup.
Kublr deploys each of the standard Kubernetes components, except for the kubelet, inside Docker containers. This ensures the solution is more portable and simplifies support for multiple operating systems and environments.
The majority of the work on the infrastructure and Kubernetes layers is done by the Kublr Agent, a single lightweight binary installed by Kublr on each node in the cluster. The Kublr Agent performs the initial setup and configuration of a node, the configuration of the operating system and Kubernetes components. It also proactively monitors the health status of the node and the components installed on it and restores them to a healthy state should any failure occur.
Kublr Control Plane
While single-node configuration and monitoring are performed by the Kublr Agent, the Kublr Control Plane is the “brain” of Kublr’s cluster management capabilities. It’s the central component that monitors and manages each of the clusters provisioned by the client. When a new cluster is created, the Kublr Control Plane generates a configuration (based on user input), initiates infrastructure provisioning, installs the Kublr Agents and sends them the configuration for each individual node.
The Kublr Control Plane serves as a single pane of glass for operations teams giving them access to each of the managed clusters from one place and enabling management of these clusters through an intuitive user interface. The Plane provides operations with centralized logging and monitoring, backup and recovery scheduling, SSO/LDAP/SAML integration, an audit file and other management functionality.
Kublr | Cluster Management
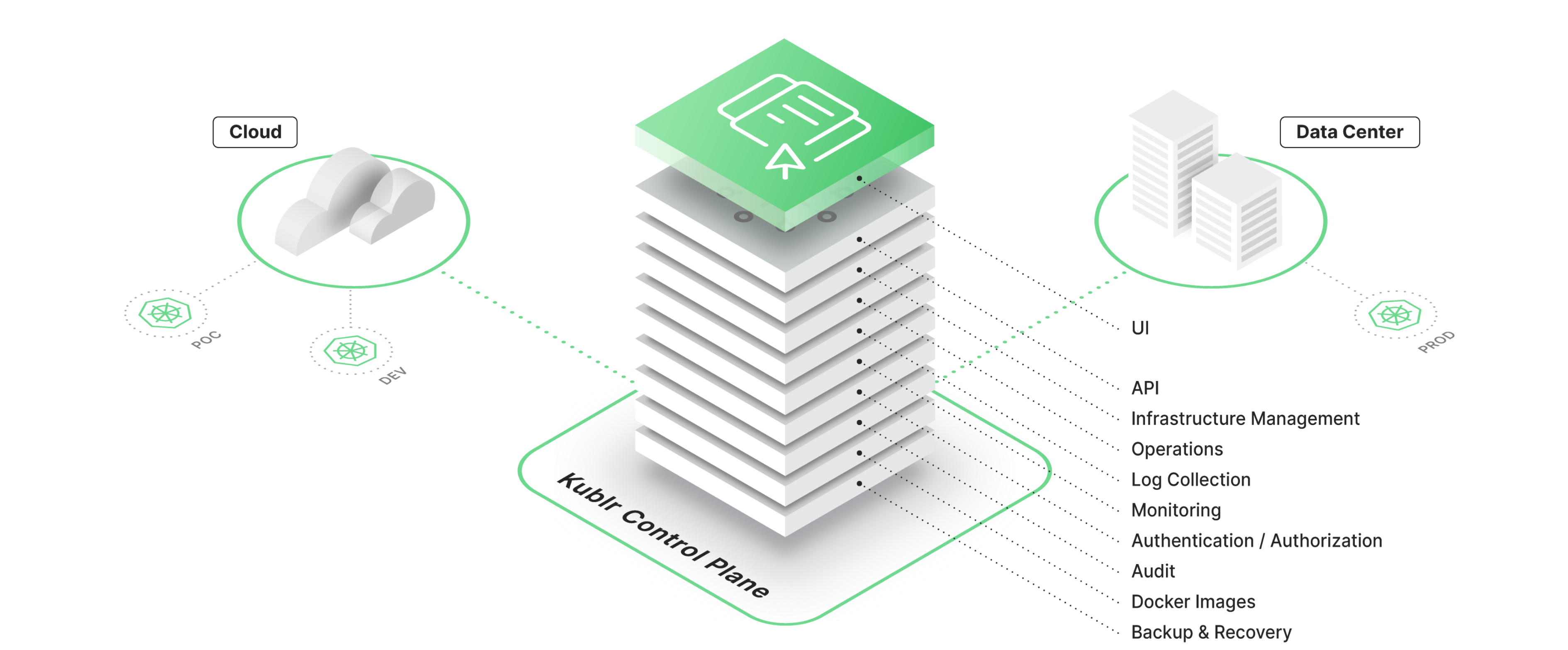
The Kublr Control Plane deploys itself into a Kubernetes cluster through a bootstrapping application. This ensures that the Control Plane and its managed components are reliable and highly available. It also allows Kublr to use standard Kubernetes tools for components management. Each of the Kublr Control Plane components, including centralized logging based on ELK, monitoring based on Prometheus/Grafana, identity broker, backup and recovery manager, optional CI/CD tools based on Jenkins/Spinnaker/Nexus, user interface and other components, is deployed using Helm packages.
The Kublr Control Plane is not required for cluster runtime. This eliminates any dependency or single point of failure. To leverage each of the capabilities of cluster management and monitoring, the Control Plane must have access to provisioned clusters over HTTPS to gather logs, metrics, events and other information, and to initiate maintenance, configuration changes or upgrade tasks on the Kublr agents.